From the Computer Errors challenge. See all 396 entries (closed)
(, Sun 24 Jun 2007, 23:46, archived)
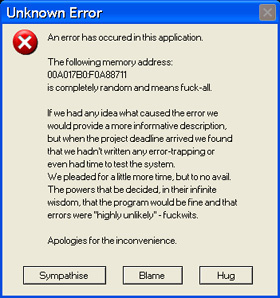
someone who occasionally calls me for advice when stuff crashes insists on reading out all those sodding numbers assuming they'll mean something to me
(,
Sun 24 Jun 2007, 23:49,
archived)
Sitting on the toilet trying to remember what the fuck those numbers mean.
/20+years of programming blog
(,
Sun 24 Jun 2007, 23:54,
archived)
/20+years of programming blog
was the most pointless debugging tool - I mean, how do you know what address the program started at?
(,
Sun 24 Jun 2007, 23:58,
archived)
parents when it set fire to the family home.
(,
Mon 25 Jun 2007, 0:05,
archived)
It's actually very useful. Programs usually load at the same address, and you can then use either the map file or load the program into memory with a debugger (on the same OS version) to find out where the address is.
In that case the error can be narrowed down considerably, although a process dump is much more useful than just an address.
The problem is moot, though; various Unixes/Vista support Address Space Layout Randomization (ASLR) to make stack overflow/code injection attacks etc harder. This changes the base load address of the process, and thus probably renders the memory address of a crash useless.
(,
Tue 26 Jun 2007, 11:50,
archived)
In that case the error can be narrowed down considerably, although a process dump is much more useful than just an address.
The problem is moot, though; various Unixes/Vista support Address Space Layout Randomization (ASLR) to make stack overflow/code injection attacks etc harder. This changes the base load address of the process, and thus probably renders the memory address of a crash useless.